1Password only decrypts what you need at the time you need it. If Molly (one of my dogs) is using 1Password to log in to SquirrelsAreEvil.net, only her SquirrelsAreEvil Login details are decrypted. Her RabbitRecipies Login, along with all her other hundreds of items, remain encrypted.
I’d like to explain why this is such an important security feature, as well as why it’s vital for Molly’s security tool to lock her 1Password data when she steps away from her computer. Limiting what is decrypted, and for how long, provides some concrete benefits, though it also raises some interesting questions. Read on to see what I mean.
Keeping secrets small
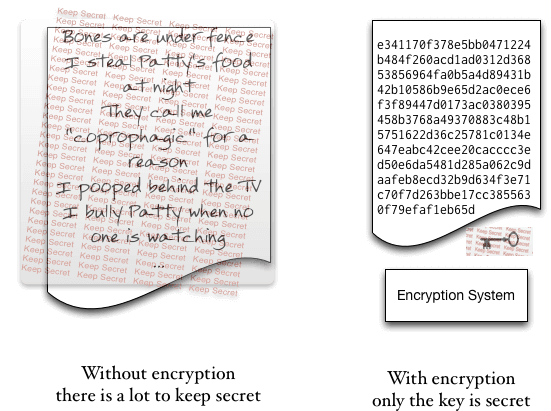
It is easier to keep sixteen bytes of data secret than it is to keep sixteen megabytes of data secret. Quite simply, it is much harder to handle and manage sixteen megabytes of data in a secure way than it is to keep just sixteen bytes secret. This is true for both people and for computer systems. You can manage your 1Password Master Password securely (in your head), but you could not do the same with all of your passwords and logins. After all, that’s why you use 1Password in the first place.
1Password enables you to turn a large secret—all of your various login information for services, secure notes, WiFi passwords, bank account details, credit cards, etc.—into a small one that you can manage—your 1Password Master Password. This is what I mean when I say that encryption allows you to turn big secrets into small ones.
Just as it is hard for a human brain to handle large secrets securely, it can also be difficult for computers. When computers are running short of working memory, they might have to make temporary notes of what is “in their heads” (writing to swap files). If a program crashes, it might write to disk some of what is in its memory (core dumps), and there are various other ways that a computer or computer program can accidentally mishandle secrets.
There are tools that systems and programmers can use to make it harder to accidentally reveal secrets, but these methods work best for little secrets. So it would be much better for a computer to only have to manage one little secret. Like you, the computer can be good at managing such secrets. Of course, a little secret (one that fits in sixteen or thirty-two bytes of data, for example) can be very very important. Note that, when I talk about “big” or “little” secrets here, I only mean the size of the data.
The way to turn big secrets into little secrets on a computer is to encrypt the big secrets with an encryption key. After that, the encryption key (or the password from which the key is derived) becomes the secret. The encrypted data, because it is encrypted, does not need to be kept secret. With the encrypted data and the key, there is no need to keep the unencrypted secret data around.
Throwing away the key
When you lock 1Password or it locks through auto-locking, 1Password throws away the key (the details are a bit more complicated as there are multiple keys and these are handled slightly differently in different versions and platforms. But let’s stick with this for now). Without the key, the encrypted data cannot be decrypted, nor is there any way to steal the key since it’s been destroyed.
The only way to decrypt data once the key has been destroyed is to make a new key, and making a new key requires your Master Password. Making keys from your Master Password is called “key derivation”. It is a subtle, but crucial, part of the design of any cryptographic system. For those interested, you may read the gory details of key derivation in 1Password 4.
When to throw away the key
When I’m working, I often get up and pace around the room. Too often I pace all the way to the refrigerator and grab a snack. This is not great for my health, but it also means that someone might walk over to my computer and take a look at the passwords I have stored in 1Password. If my computer account is accessible and if 1Password has the key, then an attacker can get at my data.
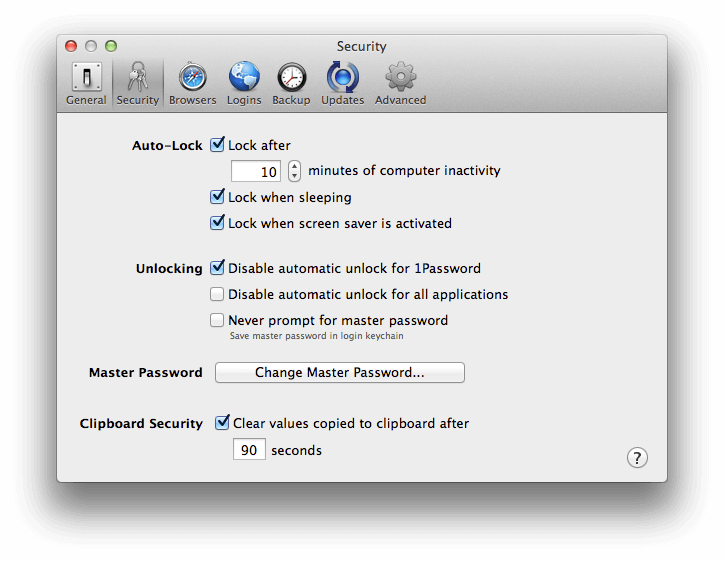
If I worked in a crowded office with people coming and going, that would be something I should be concerned about. In such a case, I would go to 1Password > Preferences > Security and set Auto-Lock to lock after only a few minutes of computer inactivity. I would also set these preferences to lock when the screensaver is activated or when the computer goes to sleep. This would mean that I might have to type my Master Password a few more times a day, but it will help immensely with keeping my secrets, well, secrets. Plus, typing my Master Password a few more times each day will help ensure that I never forget it.
Is Auto-Lock helpful?
An argument can be made that even the most aggressive auto-lock settings provide no meaningful security. I think that Auto-Lock is important, but let me first outline the argument against it.
Suppose Molly (one of my dogs) is working at her computer and runs off to chase a rabbit. She has set up auto-lock so that 1Password will be lock quickly. Molly knows that Patty (the other dog) is trying to find out where the bones are buried, a secret Molly keeps in a Secure Note in 1Password. When Molly is off chasing a rabbit, Patty goes up to Molly’s computer and sees that 1Password is locked. Patty cannot find out where the bones are buried.
But Patty came prepared. Patty doesn’t care that 1Password is locked because Patty replaces the copy of 1Password on Molly’s computer with a bogus copy of 1Password. After all, Patty has as much access to Molly’s computer as Molly would have, and that typically involves being able to install software. When Molly returns (without a rabbit) she sees what appears to be 1Password, nice and securely locked. She types in her Master Password, but the imposter version of 1Password sends that Master Password to Patty.
So the question remains, what good does locking 1Password do?
Auto-Lock is helpful
Even though it is possible for Patty to defeat Auto-Lock’s security, it is, in practice, much harder for her to do so than to simply read the data she wants when 1Password is unlocked. Even if Patty had a good imposter of 1Password at hand, and even if she could install it quickly and easily, she runs a much higher risk of getting caught because she has made large changes to Molly’s system.
There may also be barriers to installing an imposter 1Password on Molly’s machine (or otherwise changing the security system of the machine). An administrator password may be required for a normal software install. Something like Gatekeeper may detect that new software is running and ask for an administrator password. It is true that all of these can be worked around if Patty has enough time at Molly’s computer, but these all make it ever more difficult in practice for Patty to tamper with Molly’s computer in a way that will work, can be done quickly, and won’t be detected.
Raising the attack bar
We can never (well, … hardly ever) protect a computer against someone who has unsupervised physical access to it. It can be tampered with down to the boot loader. Suppose Molly is using full disk encryption (FDE) with Filevault 2 on the Mac, and she shuts down her computer completely. Patty might disguise herself as a maid (she is evil that way) and when cleaning Molly’s dog house physically replace the boot ROM on Molly’s computer. Patty can then ensure that the next time the machine boots up, it captures a copy of the disk encryption password and also installs whatever changes to the operating system and software that Patty wants.
In principle, there is little we can do practically to defend against such attacks. But it is far harder to execute an evil maid attack than to simply look at someone’s unlocked passwords. By locking 1Password, Molly makes Patty have to work that much harder (and increase her risk of getting caught) than if Molly didn’t lock 1Password.
Requiring a login password from the screensaver further increases the difficulty (and thus reduces the plausibility) of a successful attack. Using Full Disk Encryption raises the attack bar even higher.
These are cases where the good guys actually have the advantage. There are simple and relatively costless things we can do that very substantially raise the cost to the attacker.
Defending against practical attacks
We have to look not only at theoretical attacks, but the practical arsenal of attackers. We build defenses to increase the amount of work an attacker has to do. If the amount of work the an attacker has to do is beyond what that particular attacker can (or is willing to do), then we have successfully defended against that attack.
Auto-Lock features, like 1Password’s, can successfully defend against what might otherwise be common attacks. It may not defend you against a specially trained spy who has lots of time with your computer, but it will defend you against the nosy officemate who takes the opportunity to grab what she or he may when you briefly leave the room. The world has many more nosey officemates than trained spies.
Summary
We keep as little of your 1Password data decrypted as possible, and only for the shortest amount of time, because it is far easier to manage small secrets securely than large secrets. Features like Auto-Lock can’t always defend against everyone who gets access to your computer, but they do make the job of the attacker substantially more difficult. Indeed, it makes the difficulty of an attack prohibitive for the kinds of attackers we most often find for this category of threat.

 by Jeffrey Goldberg on
by Jeffrey Goldberg on
