You can now use U2F-compatible security keys as a second factor for your 1Password account.
Last year we added two-factor authentication to provide another layer of protection for your 1Password account. When this is enabled, you are prompted to enter your second factor any time you sign in from a new device.
Initially, that second factor was a time-based one-time password generated by an authenticator app on your phone. Today, I’m happy to announce a new option: We now offer support for Universal 2nd Factor (U2F)-compatible security keys. This is done via the new WebAuthn API, and we’re excited to be among the first services to adopt this new browser standard. WebAuthn is backwards-compatible with U2F, so all certified U2F security keys will work with our WebAuthn-enabled flow.
What is a security key?
Security keys are small physical devices that can be used as a second factor. Support is built into most web browsers and works with many online services like Google and GitHub.
“WebAuthn brings to life the concept of using an external security key across multiple devices and platforms, with no shared secrets among services. It’s exciting to see 1Password implement WebAuthn support to enable YubiKey hardware-backed authentication for their users”. – Derek Hanson, VP, Solutions Architecture and Alliances at Yubico
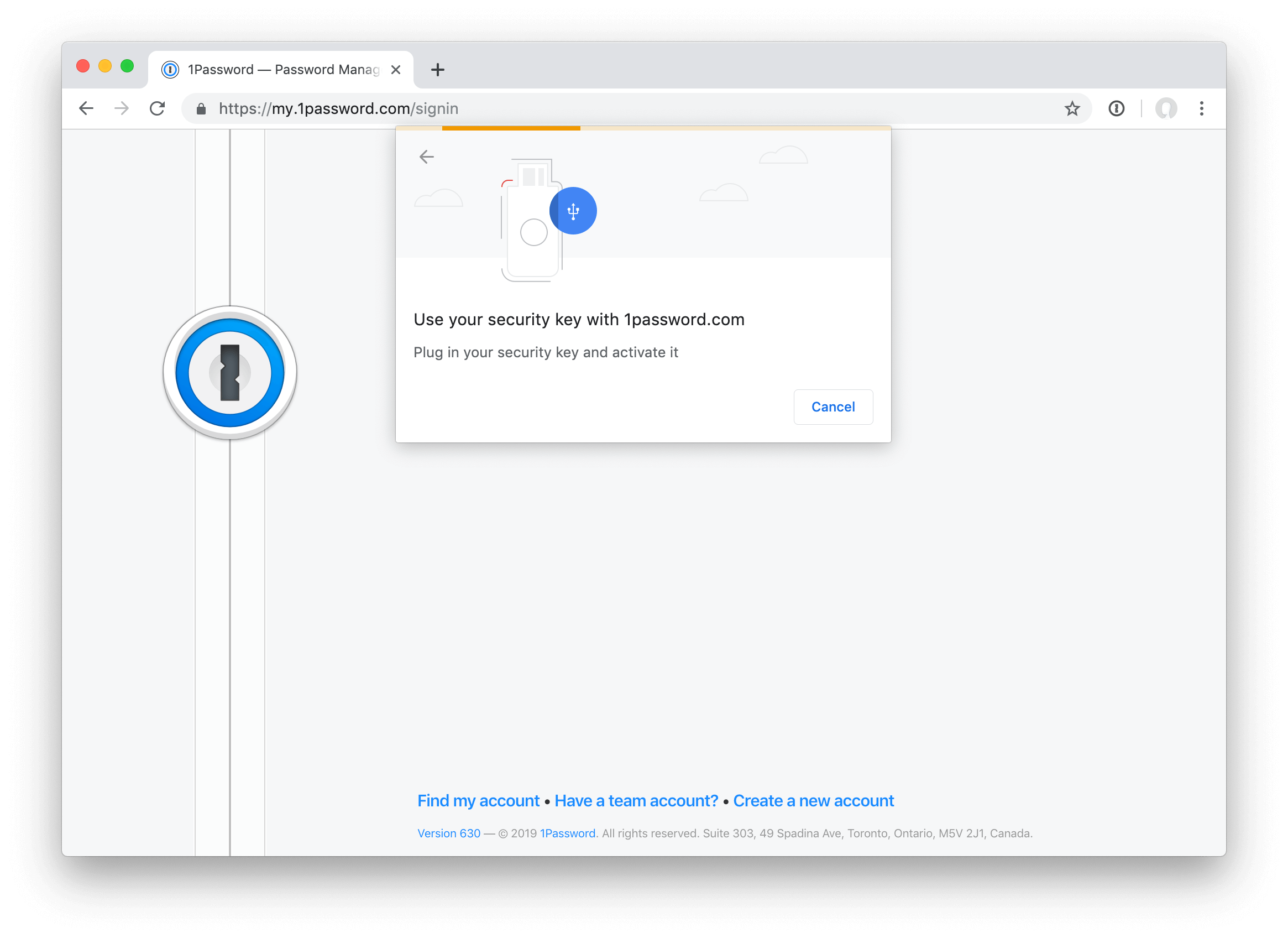
When you’re prompted for your second factor, just tap a button on your security key and you’re in. No need to find your phone, open the authenticator app, and type out the six-digit code while trying to race the countdown.
Using your key with 1Password
Security keys are currently supported on 1Password.com in the latest versions of Chrome, Firefox, Opera, and Edge. (It’s coming to Safari 13 this fall.)
So while it works great as your second factor in those browsers, for now you’ll still need an authenticator app set up to use with the 1Password desktop and mobile apps (and any unsupported browsers).
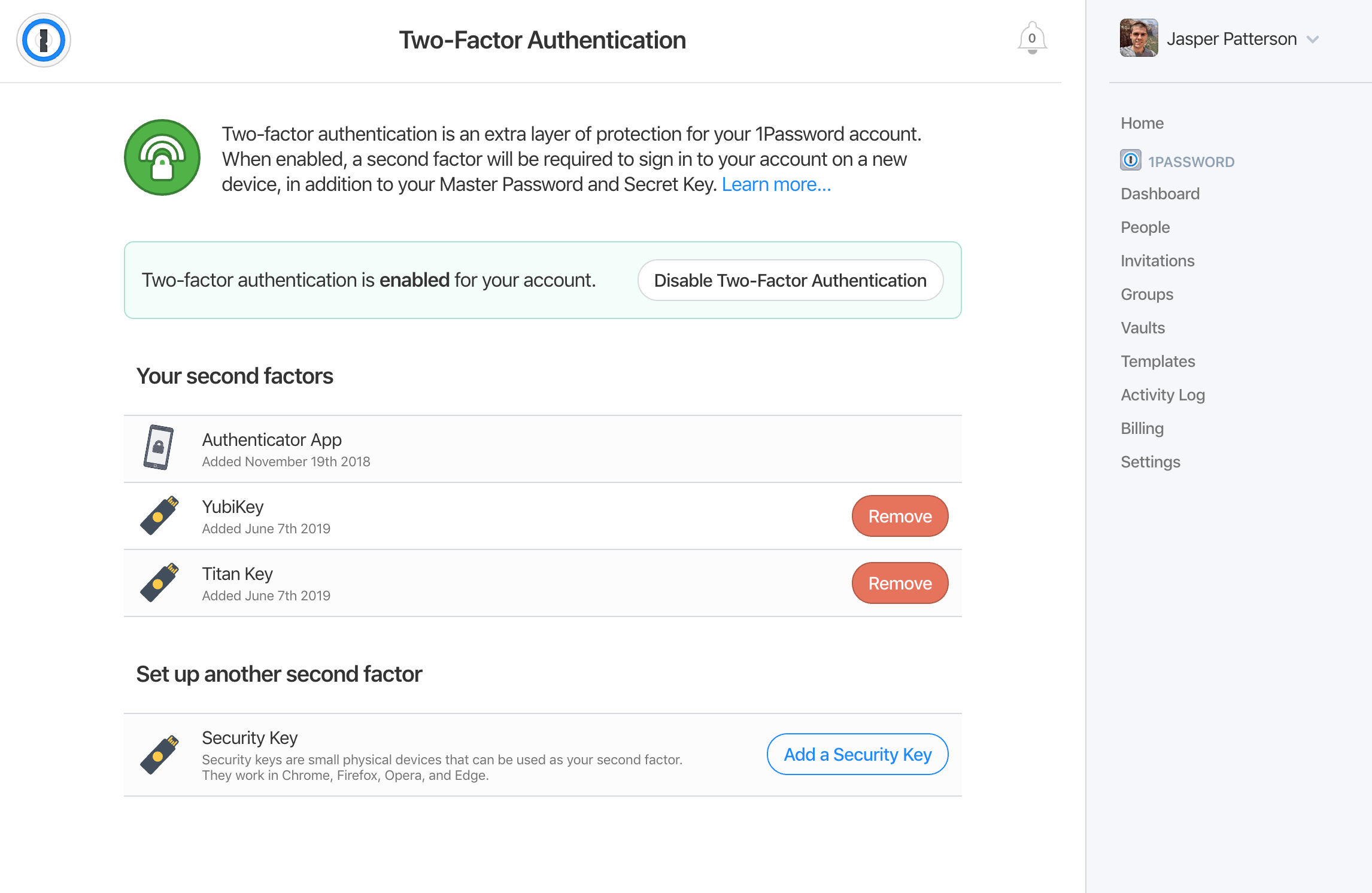
You can add your security keys now by heading over to the 1Password web app and visiting our new Two-Factor Authentication page.
Your Master Password, which is used for the encryption of your data, still remains the most important thing protecting your 1Password account. Adding a second factor does not mean you can get away with a weaker Master Password.
Where to buy a security key
If you’re interested in getting a security key, you can buy a YubiKey from the Yubico Store, Feitian keys from Amazon, or Titan keys from the Google Store. Any device that supports the U2F standard will work.
How it works under the hood
WebAuthn is a pretty neat implementation based on public key crypto, and resolves security vulnerabilities like phishing. Our server generates a random token and asks your browser to get it cryptographically signed by your security key. The browser also includes the current domain (and some other data) as part of the payload that is signed. This signed response gets sent back to our server, which will decode it; make sure the token, domain, and other data match what we expect; and finally verify the signature using the device’s public key.
 by Jasper Patterson on
by Jasper Patterson on