One phish, two phish; old phish, new phish
The easiest way to discover someone’s password is to ask them for it. There are many ways to trick people into revealing their passwords, but one of the most commonly attempted is phishing. If you can lure people to a website that looks like Paypal’s, but is actually under your control, then you can often steal their usernames and password to Paypal. This is one of the reasons why so many sites of this nature warn users to pay close attention to the URL in the location bar. “paypal.com” is not the same as “paypalc.om”.
When location bars can’t be trusted
The information in the location bar is one of the defenses against phishing, but David Vieira-Kurz of Majorsecurity discovered a bug in AppleWebkit on the iPhone, iPad, and iPod Touch that gets around this defense. AppleWebkit is the technology that underlies not only Mobile Safari but pretty much every app that has a built in web browser. This bug allows a malicious website to place a false URL in the location bar of the browser. Now is probably a good time to point out that 1Password on your iOS device protects you against this, and I’ll get into the how and why below.
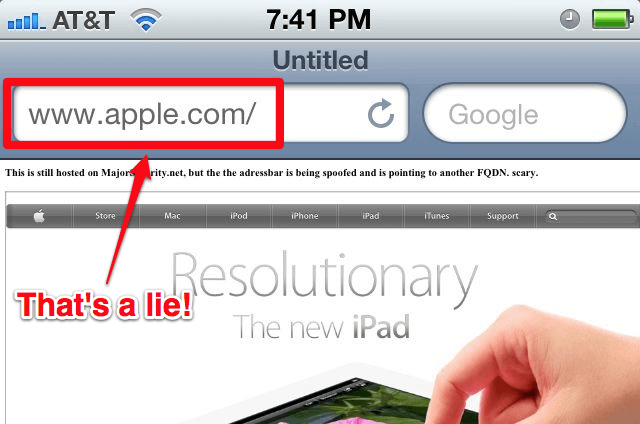
Majorsecurity has set up a page to demonstrate this bug (editor’s note: this page is no longer available). If you visit that with Mobile Safari and tap the Demo button you will see a page that looks like Apple’s homepage and will falsely contain www.apple.com in the location bar. I haven’t investigated how this trick would interact with the website authentication provided by SSL/TLS (when you connect to a secure “https” site), but as people don’t always check whether they are connected to an https site, this new bug could definitely lead to more successful phishing.
1Password’s phishing defense
1Password provides defense against phishing by carefully checking the domain to which the browser is connected. So it will only report a match for your Login for, say, Paypal when you really are visiting a site in the paypal.com domain. As a quick demonstration of this, I’d like to show that 1Password on my iPhone correctly recognizes the Majorsecurity demonstration as being on majorsecurity.net and not as the apple.com site it masquerades as.
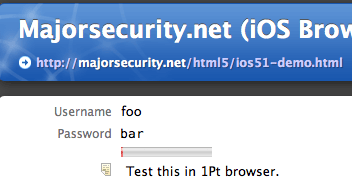
I already have a number of Logins for the domain apple.com, but I created a new Login for majorsecurity.net. The username and password I set up for that are “foo” and “bar”. (I think you will understand if I’m not going to tell you my username and password at Apple.com.)
When I go to Majorsecurity’s demonstration page using 1Password on my iPhone, then tap their “demo” button, I am brought to a page that looks very much like Apple’s homepage. (Majorsecurity puts a little warning text in there to help you see that it is actually not Apple’s real home page.) And when I tap the 1Password globe to bring up the credential for the site, 1Password correctly gives me the username and password I’ve set up for majorsecurity.net; it does not bring up any of my apple.com Logins. 1Password knows what site I’m talking to despite the tricks that the site uses.
Ask and you shall receive
As you can see, 1Password makes it harder for you to fall victim to a phishing attack, but it can’t, for example, prevent you from revealing your passwords over the phone or in other ways.
Let me tell you about my own deviousness. Sometimes when I talk about password security to a group of people, I offer a challenge that I will be able to discover a password of their choosing. When I get a volunteer, I ask them to write the password down on a piece of paper, fold the paper and bring it to me. For a little while I go through a show of fiddling with my laptop, and I definitely ask them to use a password that doesn’t reveal a personal secret. (A surprising number of passwords people pick are things like “ILoveJenny”.) Finally, after enough mumbo-jumbo, I simply read the password that the victim so conveniently wrote down and gave to me. This is when I announce that the easiest way to discover someone’s password is to ask them for it.

 by Jeffrey Goldberg on
by Jeffrey Goldberg on

